Need to Know: Cybersecurity

Editor’s Note: Welcome to Future’s third edition of Need to Know, a series exploring complex topics like blockchain, 5G, and artificial intelligence — and how they apply to each industry served by our websites and magazines.
Chris Wysopal is a hacker who was quoted in a Washington Post column about the state of internet security (or perhaps we should call it Insecurity). In May, Wysopal — also known by his hacker name, Weld Pond — joined several others in a return visit to Capitol Hill, where 20 years earlier they’d testified in a congressional hearing about the insecurities of software and networks.
Their 1998 appearance helped put the issue of cybersecurity on the national stage. A central part of their 2018 message is that digital security isn’t much better today.
COSTLY AND DANGEROUS
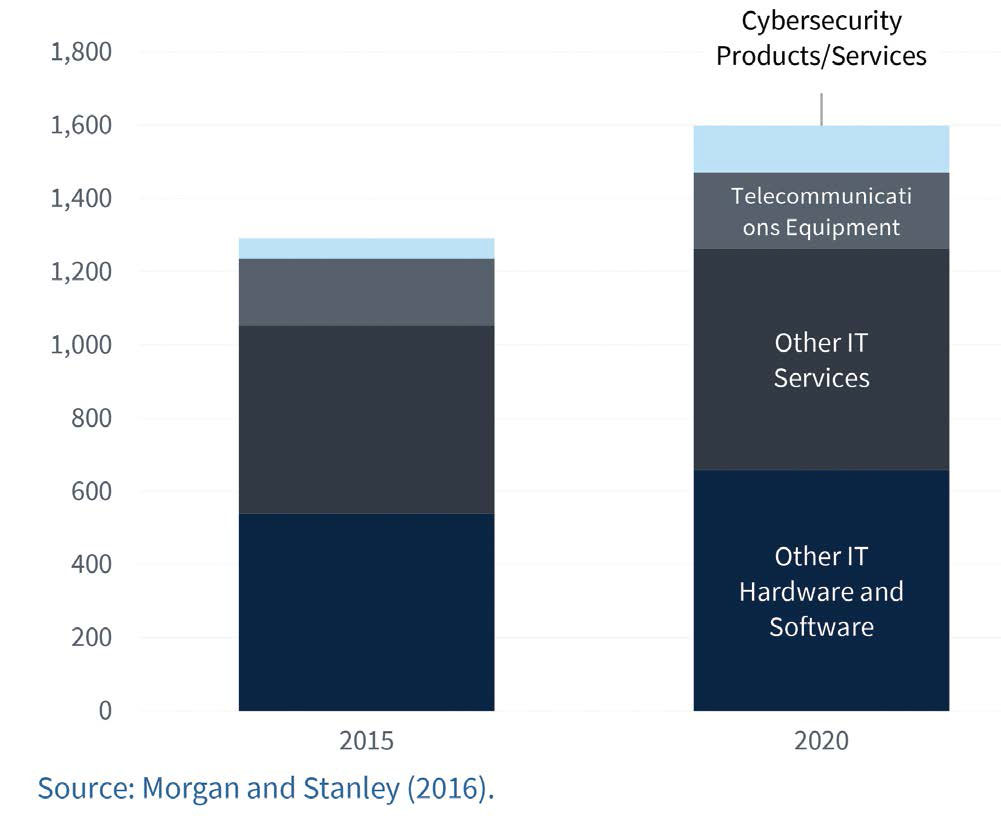
Malicious cyber activity cost the US economy between $57 billion and $109 billion in 2016, according to the White House Council of Economic Advisors. Cyber threats are ever-evolving, and the sophistication of adversaries keeps growing. But, according to the White House report, the private sector may, for any number of reasons, be tempted to underinvest in cybersecurity.
National security officials echo the concern.
“Our daily life, economic vitality and national security depend on a stable, safe and resilient cyberspace,” says the US Department of Homeland Security in explaining why it devotes a large Web resource to the topic.
Tools and ideas to transform education. Sign up below.
The department this spring released a strategy hoping to help reduce vulnerabilities, build resilience, counter malicious actors, and make the ecosystem more secure. It identifies 16 “critical infrastructure” sectors where a loss of networks would have a debilitating effect on the country. But even trying to define the sectors demonstrates how broadly the subject touches every corner of American life; they range from commercial facilities and manufacturing to the communications sector and health care.
Homeland Security took particular note of a growing concern about the threat of “wide-scale or high-consequence events” that could cause harm or disrupt services on which the economy and millions of people depend. “Sophisticated cyber actors and nation-states exploit vulnerabilities to steal information and money and are developing capabilities to disrupt, destroy or threaten the delivery of essential services.”
How might your own business be hacked? A threat can come via denial of service attacks; destruction of data and property; disruption of business, perhaps for ransom; and the theft of your proprietary data, intellectual property, and financial and strategic information. Reports of data breaches and cyber attacks are everyday news. Lewis Morgan on the IT Governance Blog curated more than 60 such stories in the month of May and counted the total of breached records that month at more than 17 million — “actually quite low when compared with previous months.”
In 2018, virtually every major and minor business or organization relies on the global, interdependent IT ecosystem. The degree to which leaders take the subject seriously could, in the long term, determine the survival of those enterprises.
To learn what trends businesses should be watching, we turned to several sources approaching the topic from various angles.
THREATS IN BURSTS
In its 2018 Annual Cybersecurity Report, Cisco said malware is definitely becoming more vicious and harder to combat. “We now face everything from network-based ransomware worms to devastating wiper malware,” the company stated. “At the same time, adversaries are getting more adept at creating malware that can evade traditional sandboxing.”
While encryption can enhance security and is used by roughly half of global Web traffic, Cisco continued, encryption provides bad actors with a powerful tool to hide command-and-control activity. “Those actors then have more time to inflict damage.”
Artificial intelligence may help. “Encryption also reduces visibility. More enterprises are therefore turning to machine learning and artificial intelligence. With these capabilities, they can spot unusual patterns in large volumes of encrypted Web traffic. Security teams can then investigate further.”
Cisco made note of several other trends and findings:
■ Short, pernicious “burst attacks” are growing in complexity, frequency, and duration. “In one study, 42% of the organizations experienced this type of DDoS [distributed denial of service] attack in 2017. In most cases, the recurring bursts lasted only a few minutes.”
■ Many new domains are tied to spam campaigns. “Most of the malicious domains we analyzed, about 60%, were associated with spam campaigns,” Cisco reported.
■ Security is seen as a key benefit of hosting networks in the cloud. “The use of on-premises and public cloud infrastructure is growing. Security is the most common benefit of hosting networks in the cloud,” the security personnel respondents say.
■ One bad insider can be a big threat, and a few rogue users can have a huge impact. “Just 0.5% of users were flagged for suspicious downloads. On average, those suspicious users were each responsible for 5,200 document downloads.”
■ It’s not just your IT assets that are at risk. Expect more attacks on operational technology as well as the Internet of Things. “Thirty-one percent of security professionals said their organizations have already experienced cyber attacks on OT infrastructure.”
■ The multi-vendor environment affects risk. “Nearly half of the security risk that organizations face stems from having multiple security vendors and products.”
IOT RANSOMWARE
Another observer taking stock is Aidan Simister, the global SVP for Lepide Software. Writing in a post on the CSO website, he too predicts artificial intelligence will take a bigger role. But while AI may help the good guys, he notes, hackers too can use it to launch more sophisticated cyberattacks. Further, new strains of malware can work around “sandbox” defensive techniques, waiting until they are outside the sandbox before executing their malicious code.
Meanwhile, Simister agrees that the “Internet of Things” could become more of a target for ransomware, with hackers targeting power grids, factory lines, smart cars, or home appliances to demand payment. Many businesses, Simister predicted, will not comply with the European Union’s new General Data Protection Regulation on data protection and privacy (the thing you’ve been getting all those emails about). He predicts some companies will choose to ignore it, accepting the risk.
We’re also likely to see a growing number of companies adopt multi-factor authentication in response to data breaches involving weak, stolen or default passwords.
He expects that more sophisticated security strategies may find wider adoption. These may include the use of “remote browsers”; deception technologies that imitate a company’s critical assets; systems to spot and identify suspicious behavior; better network traffic analysis; and “real-time change auditing solutions” that do things like detect abuses of user privileges or suspicious activity in files and folders.
But Simister also sees the risk of more attacks backed by hostile governments; in response he predicts more efforts to train staff and to develop international sharing of information.
PRIVACY PARADOX
One change in mindset visible in the market is a de-emphasis on the idea of “perimeter security.” “You are not safe behind the perimeter, because the perimeter itself no longer exists,” Akamai argues on its website. “Today’s world is cloud- and mobile-driven, and the traditional moat-and-castle approach to enterprise security is no longer applicable for modern business practices.”
With applications hosted in various places and a work force on the move, the company argues, there is no longer a delineation between inside and outside the network. “As a result, seemingly every week there are new reports about high-profile data breaches and cyberattacks.”
Akamai chief technology officer Charlie Gero argues in favor of what he calls zero trust security architecture. “Companies must evolve to a ‘never trust, always verify’ zero trust model to secure against the wide variety of threats that exist and are constantly evolving,” Akamai states.
Looking at the consumer economy more broadly, cybersecurity is only likely to become more crucial, thanks to ongoing developments in areas as diverse as cryptocurrency, interactive smart speakers and mobile payments.
For example, a major trend toward platform personalization — whether it be on Facebook or Spotify, Wave or NextDoor — raises the privacy stakes. Venture capitalist Mary Meeker of Kleiner Perkins notes the massive amount of personalized data that people have put into such platforms.
That data, she said in remarks at the Code 2018 conference, improves engagement and leads to better experiences for consumers — but it also helps create what she calls a privacy paradox: “Internet companies are making low-price services better in part from user data. Internet users are increasing their time on Internet services based on perceived value. Regulators want to ensure data is not used improperly, and not all regulators think about this in the same way.”
Regulatory considerations are thus a big, uncertain element in this picture.
THE WEAK HUMAN LINK IT
expert Wayne Pecena, who works in the broadcast and education sectors, says security should be an ongoing process. Yet at many business, unfortunately, it tends to be treated as a one-time, set-it-up-and-forget-it event.
Pecena is assistant director of information technology for educational broadcast services at Texas A&M University and director of engineering for KAMU public radio and television; he says cybersecurity never has an end.
“It is a continuous process of monitoring, evaluation, analysis and prevention as the threat landscape is always in a state of change and evolution,” he said. “I would also not lose sight of the past, as ransomware, phishing [and] distributed denial of service will likely continue at an accelerated pace. As cloud services and applications continue to expand, I would also keep the cloud cybercrime landscape or Cybersecurity-as-a-Service on my radar.”
In Pecena’s experience, most organizations do spend plenty of time and money in protecting their IT environment, but often the simplest areas can be overlooked while the focus is on higher-tech matters. “Social engineering remains one of the largest threats to an organization, and the human factor remains a weak link. The Internet of Things movement brings challenges, as most of these types of devices lack any real internal security capability and instead rely on external protection means.”
He also finds “crypto-mining” a fascinating area of concern as computing resources are hijacked for someone’s bitcoin mining applications. “Not necessarily destructive — like DDoS or ransomware — to an organization, [but] host computing resources can be [affected] such that legitimate application use is impacted. Malicious mining scripts can easily be picked up from a casual website visit, and this opens a new area for antivirus protection software.”
Pecena said for him this recalls the days of desktop computers being unknowingly hijacked to serve music or distribute porn. Those well-meaning hackers who returned to Washington recently hoped to draw attention once again to the issue of digital security. At least one pushed for government to play a larger role. But another said companies also need to take advantage of the tools and knowledge that are already available.
It was Robert Mueller — yes, that one — who is credited with saying back in 2012 that there are only two types of companies: those that have been hacked and those that will be hacked. Today that wisdom is often updated to read: “There are two types of companies: those that know they’ve been hacked, and those that don’t know they’ve been hacked.”
Manage accordingly.
FIVE CYBERSECURITY SAFEGUARDS FOR SCHOOL DISTRICTS
Here are five best practices for districts trying to maintain a balance between adhering to privacy regulations and meeting demands for transparency as they gather, share, and protect K–12 information.
1 REVIEW FERPA COMPLIANCE. Public school districts are obligated to notify students and parents annually of their rights under FERPA, so a basic review of compliance—including whether your district meets the requirements of the accompanying Protection of Pupil Rights Amendment—can help maintain good data management habits. You can sign up for updates on both websites.
2 PRIORITIZE DATA. Critical information, including personnel and payroll records, student medical histories, and data that contains information such as Social Security numbers, must be carefully stored and securely protected. General information such as school lunch menus, graduation rates, and calendar information does not need to be protected.
3 USE SOPHISTICATED PASSWORDS. A surprising number of breaches of school data have occurred because of imperfect passwords. This is a simple but often overlooked fix for protecting critical information. All personnel and vendors need to be trained in the importance of using sophisticated passwords.
4 ENSURE SECURE STORAGE. Because districts increasingly store student and personnel information on servers or in the cloud, it’s crucial to find the safest data storage solution to meet your district’s needs.
5 SCHEDULE AN AUDIT. When should you have your district’s cybersecurity audited? Surprisingly, it’s when you think you’ve done everything that needed doing. An audit can help determine if your efforts have paid off and find any weaknesses before a breach occurs.
SOURCE: FIVE CYBERSECURITY SAFEGUARDS FOR SCHOOL DISTRICTS FROM SUNGARD K–12.
